April Fools' Day pranks fade away quickly, but unfortunately, cybercriminals remain active all year round.
Springtime is a peak season for cyberattacks—not due to careless teams, but because the hustle and distractions of busy workdays create perfect opportunities for scams to slip through unnoticed.
Here are three sneaky scams targeting even the most alert and hardworking employees right now.
As you review these examples, ask yourself: Would my team consistently spot these threats before any harm is done?
Scam #1: Fraudulent Toll or Parking Fee Texts
An employee receives a text reading:
"Unpaid toll balance: $6.99 due within 12 hours to avoid late charges."
The message references real systems like E-ZPass, SunPass, or FasTrak based on location, with a small fee that doesn't raise suspicion. In the middle of a busy schedule, the employee clicks, pays, and moves on.
But the link is a scam.
In 2024, the FBI logged over 60,000 complaints about fake toll texts, with a staggering 900% increase reported in early 2025. Cybercriminals have created more than 60,000 counterfeit domains mimicking official state toll agencies, highlighting just how lucrative these scams have become. Shockingly, some texts even targeted residents in states without toll roads.
The scam's success lies in small charges feeling harmless and the common experience of toll or parking usage, which makes the message believable.
The key defense: Authentic toll agencies never demand immediate payment via text links. Reliable companies enforce strict policies that prohibit paying through text links. When in doubt, employees should always visit the official website or app directly. Importantly, they should never respond to such texts—not even to opt out—as replies confirm the phone number is active and invite more phishing attempts.
Stop convenience from becoming your downfall—follow processes to stay protected.
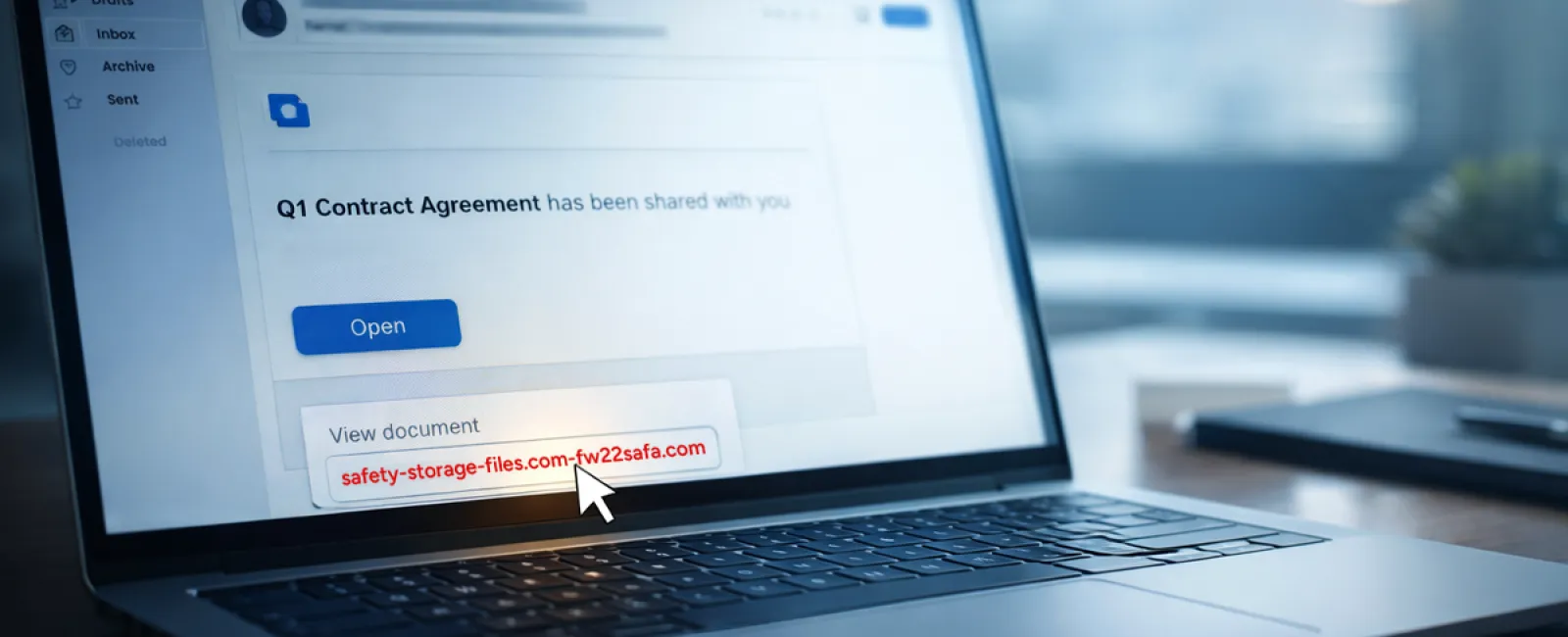
Scam #2: Fake "Your File Is Ready" Notifications
This scam blends seamlessly into daily workflows.
An employee receives an email indicating a file has been shared—often appearing as a DocuSign contract, a OneDrive spreadsheet, or a Google Drive document.
The sender's name and email formatting look legitimate, mimicking typical file-share alerts.
The employee clicks, is prompted to sign in, and unknowingly provides their work credentials.
Attackers then gain access to your company's cloud systems.
Phishing campaigns exploiting trusted platforms like Google Drive, DocuSign, Microsoft, and Salesforce surged by 67% in 2025, according to KnowBe4's Threat Labs. Phishing via Google Slides alone jumped over 200% within six months.
Employees are seven times more likely to click links from trusted services like OneDrive or SharePoint than from unfamiliar emails, since the notifications appear genuine.
Worse, attackers now create files inside compromised accounts and share them through these platforms, sending notifications from legitimate servers that bypass spam filters.
How to guard against this: Train staff not to click links in unexpected file-share emails. Instead, they should log in directly through official web portals to confirm files' existence. IT teams can minimize risk by restricting external file-sharing permissions and activating alerts for unusual login activities—settings that can be configured in roughly 15 minutes.
Simple habits yield powerful protection.
Scam #3: Deceptively Polished Phishing Emails
Gone are the days of obvious phishing emails riddled with poor grammar and errors.
A 2025 study revealed AI-crafted phishing emails received a 54% click rate—over four times higher than human-written phishing attempts.
These scam emails seamlessly reference real companies, job titles, and internal processes, scraped from publicly available online sources like LinkedIn.
Targeting has become sophisticated and departmental: HR and payroll teams encounter fake employee verification requests, finance staff receive forged vendor payment instructions, and in tests, 72% of recipients engaged with vendor impersonation emails—90% more than other phishing types.
The emails are calm, believable, and urgent without being dramatic, appearing as a typical workday message.
Effective defenses include: All requests involving credentials, payment updates, or sensitive data must be verified via a second channel—whether a phone call, instant message, or in-person. Employees should always hover over sender addresses before clicking and view email domains carefully. Also, treat any email that creates a sense of urgency as a red flag.
Genuine security informs without instilling panic.
The Bottom Line
These scams thrive because they exploit familiarity, authority, timing, and the tempting belief that "this will only take a moment."
The true vulnerability isn't careless employees but systems that expect everyone to always pause and make perfect decisions under pressure.
If a single rushed click could jeopardize your business, it's not a people problem—it's a process problem.
And process problems are solvable.
How We Support Your Security
Most business owners want solutions without turning security awareness into another complex project or the sole responsibility of one person.
They want peace of mind knowing their business isn't silently at risk.
If you're worried about your team's exposure—or know another business owner who should be—you're invited to a straightforward discovery session.
During the call, we'll cover:
- The current cyber threats businesses like yours face
- Common ways risks enter through everyday work habits
- Practical steps to reduce threats without disrupting productivity
There's no pressure and no scare tactics—just an opportunity to identify vulnerabilities and explore effective options.
Click here or give us a call at 332-217-0601 to Speak to an Expert.
If this message isn't relevant to you, please forward it to someone who would benefit. Awareness alone can turn "would have clicked" into "nice try."